WHAT IS SOCIAL ENGINEERING?
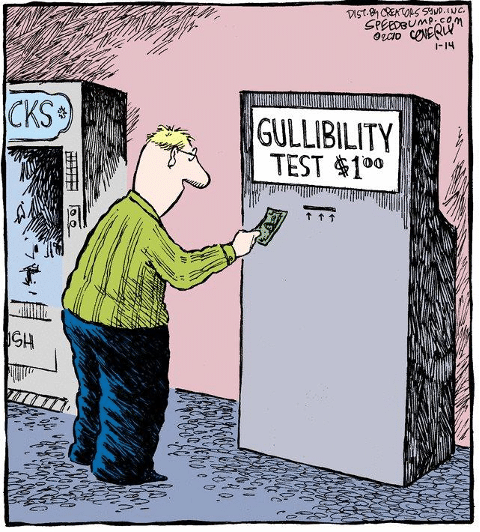
At its root, social engineering is exploiting human nature. Humans are innately trusting, and they frequently try to assist others in order to prevent conflict. Taking advantage of our social trust in order to accomplish any form of harmful objective is a key part of social engineering.
Figure 2 – Your Employee who Held the Door Open for us
Social Engineering generally falls into four (4) attack vectors:
Phishing (email-based)
Vishing (voice/phone-based)
Smishing (text-based)
Physical (in person)
To go over each of these attack routes in depth would require a separate blog post. We’re going to focus on social engineering from a physical standpoint for the sake of this blog.
When social engineering individuals during a physical breach attempt, several strategies and phases are used. These are some of them:
- Using a pretext (creating a story to add legitimacy)
- False identity (posing as an employee of the company targeted, or a maintenance worker, contractor, visitor from another office, etc.)
- Redirection/Distraction (shifting your target’s attention away from yourself/your actions and towards something else)
- Subversion of the Mind (verbally manipulating folks to obtain bits of information)
- Piggybacking/Tailgating (following another person closely, usually to gain access through a secured entry, such as a card reader-controlled door)
- De-escalation techniques (de-escalating a situation, or an individual, such as an irate guard)
SOCIAL ENGINEERING FROM A PHYSICAL PERSPECTIVE?
Let’s take a look at how a typical physical breach may go, based on what we’ve learned so far:
In the pretexting phase of the engagement, I normally spend several hours researching the company before trying a physical breach, whether covert or overt. I’ll browse through social media sites like LinkedIn, Facebook, YouTube, and Instagram for information about the company’s culture, employee kinds, and photos of employee uniforms or badges. Using satellite photos or publicly available building interior maps, I am frequently able to determine building layouts. This aids in the creation of a credible pretext. I may even call the main phone line in an attempt to elicit whatever further information I can (through subversion or impersonation), such as whether more people are involved.
I usually spend several hours on-site watching the premises, which includes the personnel and their traffic patterns, staff meeting spots such as smoking, break, and lunch areas, and any additional access or exit doors. This frequently allows for adequate tailgating/piggybacking into the main building or into critical areas within the facility. I’ll use tactics like redirection/distraction (like being on the phone) to avoid answering pesky questions like “Who are you?” or having my hands full of donuts so I can’t quite reach the card reader (who doesn’t like donuts? ), or even being a polite gentleman and allowing others to go ahead of me (after you!).
HOW TO PROTECT YOUR BUSINESS AGAINS THIS?
Teach your employees, end-users, and staff about security. Make friends with your customers. They are frequently the first line of defence, particularly when it comes to physical security and social engineering. Make sure your users know how to contact building security or guards if your company uses them. Make it a point for the building security/guards to introduce themselves to your staff so that they feel more at ease in the event that they need to call.
To maintain general awareness of core security concepts, it is critical to communicate security awareness materials on a regular basis in a variety of ways. Attacks like these are becoming more common. There are sure to be a lot of new faces around the office as more people return to the office after more than a year of working from home. That once-a-year PowerPoint presentation is no longer sufficient. Monthly awareness communications should be sent out, ideally using various distribution means each time. Make your statement loud and clear. Here are some suggestions for improving awareness training:
- Informative emails
- Informational posters
- Cards near enrty and exit doors reminding staff not to tailgate.
HOW IT WORKS
GET AN IT SOLUTIONS QUOTE
We’ll chat about your business, how you use technology, and what you want to get out of IT.
Lets Talk

We’ll chat about your business, how you use technology, and what you want to get out of IT.
Choose Your Plan

If we’re the right fit, you’ll choose the IT service agreement that works best for your organization.
Start Your Experience

Within days, you’ll be experiencing IT like never before.